- History
- Military
A range of breakthrough technologies are emerging today that have the potential to radically change how we fight and deter threats across all conflict domains—air, land, sea, space, and cyber. Artificial intelligence, directed energy, robotics, and machine learning are just a few examples. Significantly, unlike in previous decades, defense-relevant technologies are increasingly being developed in the commercial technology base rather than in classified government R&D programs. States and non-state actors alike are now able to purchase, copy, or steal advanced technologies and exploit their military applications in unprecedented ways. This proliferation of technology is diffusing military power, and the U.S. must re-calculate the current and anticipated relative military strength and capabilities of our enemies and competitors around the world.
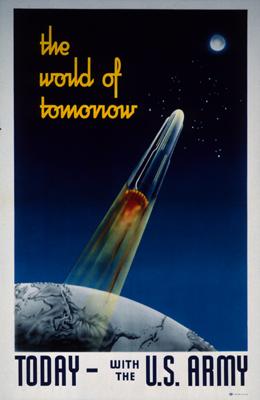
How should the U.S. respond to this “leveling of the playing field” and the resultant waning of our comparative advantages? In the past, the U.S. has responded to such situations with so-called offset strategies that leveraged America’s edge in technology. We innovated to offset the disadvantages we faced. For example, when NATO in the early 1950s found itself outmatched in conventional force strength compared to Warsaw Pact nations, President Eisenhower responded with the New Look strategy that bolstered U.S. nuclear deterrence capabilities. By fielding an increasingly capable arsenal of nuclear weapons both at home and in forward deployed locations, the U.S. effectively offset the advantages of superior Soviet conventional forces and arguably helped deter Soviet aggression and adventurism in Europe.
A second offset was triggered after the Soviet Union attained near parity in nuclear weapons with the U.S in the 1970s. Moscow’s advances, and its strength in conventional forces, led to concerns in Washington that our capability to deter Soviet aggression was degrading. So Secretary of Defense Harold Brown and Defense Undersecretary Bill Perry initiated investments in stealth technology, long-range precision-guided munitions, and advances in intelligence, surveillance, and reconnaissance (ISR) systems. The fruits of these investments were made clear in the 1991 Desert Storm campaign and the 2003 invasion of Iraq, up through the toppling of Saddam Hussein’s regime.
Russia’s and China’s significant investments in military modernization programs in recent years, such as their increasing anti-access and area denial systems capabilities, prompted Secretary of Defense Chuck Hagel to call for a “Third Offset Strategy” in 2014. Hagel argued we must exploit advances in areas like robotics, autonomous systems, miniaturization, big data, and advanced manufacturing, to counter our competitors’ advances.1
The technologies developed and deployed as part of previous offset strategies helped the U.S. achieve their intended purposes of deterring war with a major power. The advances in technology being pursued as part of the third and latest offset strategy promise to help the U.S. respond to emerging threats posed by China, Russia, and other “pacing competitors” that may arise in the coming decades. But technology advances alone do not constitute a strategy, and the advantages we can expect them to provide us will be short-lived when compared to previous offsets. It’s not that technology isn’t critical to sustaining an advantage in military strength, but it is better viewed as a constantly evolving means to achieve strategic ends, and not a static end in itself.
The democratization of access to cutting-edge technology is challenging the efficacy of traditional determinants of military power. Classic realist theories of international relations posit that a state’s capacity to raise and employ a powerful military is well predicted by aggregate wealth and resources. In an anarchic international system where states must ultimately rely on themselves to survive and maintain their position, they will theoretically be driven to field the best military forces possible given their resources.2 Realist explanations for what predicts a state’s military capabilities were largely accurate in the past: Strong states like the U.S. could develop and field the very best technology, while weaker states—not to mention non-state actors—were denied access to the most advanced military technologies given the barriers to entry that marginalized all but the most wealthy and powerful states.
But conditions have changed dramatically since the U.S. successfully competed with its Cold War rivals in the last century. These earlier struggles for technological dominance played out in secretive national labs and in other classified government sponsored domains where the nation’s best and brightest scientists and technicians worked. Today, by contrast, state of the art technology with military applications is being developed in the commercial sector more rapidly and at lower costs by the world’s leading experts incentivized to work for private companies rather than for the military or government. States with far fewer resources and non-state groups like ISIS, al-Qaeda and others can purchase or otherwise appropriate many of these technologies. Thus, the advantages the U.S. maintained throughout the Cold War due to its vastly superior wealth and resources are now being diminished. The proliferation of these dual-use technologies has changed the calculus of how we should assess capabilities of states and non-state groups today and going forward.
We cannot predict with any certainty what the disruptive military technologies of the future will be. But we should expect that these technologies will be developed faster and more iteratively, and will be more widely available than ever before. Given this, military capability in this century will turn less on developing a particular “game changing” technology that provides long term comparative advantages—like stealth and precision munitions did in the past—and more on the speed in which states and non-state groups alike can adapt and change to leverage emerging technological breakthroughs for maximum effect.
The U.S. military will find it challenging to innovate and change at this speed. Our current defense acquisition processes, for example, work well when we can anticipate the outcomes we want years in advance, such as incremental improvements in submarines, aircraft carriers, and main battle tanks. But these acquisition processes break down when the solutions we need to deploy are not known years ahead of time—and that’s precisely the case for many of today’s dynamic emerging threats. We must adapt and augment our current acquisition processes to reflect the critical need for speed and agility in procuring and fielding the latest advances in technology. And lastly, we must find new and creative ways to harness the potential of our best and brightest minds and bring them back to the table in support of our national security.3
1 See Chuck Hagel, “Secretary of Defense Speech,” Reagan National Defense Forum Keynote, Ronald Reagan Presidential Library, Simi Valley, CA (November 15, 2014).
2 Kenneth Waltz (1979) provides the core realist assessment of how a state’s resources and relative material advantages predict its ability to prevail in conflict between states.
3 For example, “Hacking for Defense,” a university course developed by Steve Blank, Joseph Felter, and Peter Newell and piloted at Stanford in 2016, provides opportunities for graduate students from all disciplines to work on pressing problems facing the DoD and the intelligence community using powerful Lean innovation methods. Their book, Hacking for Defense: Lean Innovation, Speed, and the Future of War, is forthcoming from Wiley Press.