- Law & Policy
- Regulation & Property Rights
- Security & Defense
- Terrorism
- Economics
O
fficials, lawyers, judges, and pundits have all overlooked an important issue in the proposed breakup of Microsoft: How would splitting apart the software giant affect U.S. national security?
 |
|
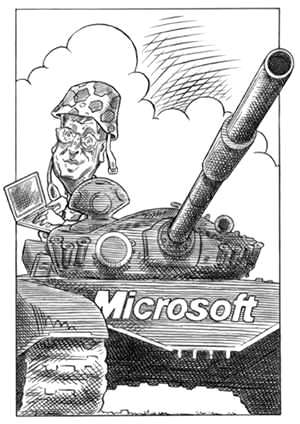
Illustration by Taylor Jones for the Hoover Digest. |
It is unfortunate that this issue has slipped between the cracks because the Microsoft case raises larger questions for U.S. policy. Today “information infrastructures”—of which software is a key component—are prime targets for attack by hostile armies, intelligence services, terrorist groups, and criminal organizations. The ability of the United States to defend itself successfully against attack may depend on a strong U.S. information industry. Yet it may be impossible for U.S. companies to achieve such strength without becoming, at least in the eyes of some critics, monopolies.
Also, in the Information Age the U.S. military needs to work more closely than ever with the private sector. The defense of the country will depend on whether companies adopt measures that make them more resistant to attack. It would be hard for the government simply to mandate that industry adopt these measures. Rather, government and industry must cooperate.
Yet current U.S. policies often seem aimed at exactly the opposite goals. They make it harder, not easier, for American firms to dominate their markets and have made relations between government and industry worse, not better. The justice department’s proposed settlement for the Microsoft antitrust case is an example. Breaking up Microsoft could create threats to U.S. national security that would outweigh any of the purported economic benefits. Also, a ruling against Microsoft could set legal precedents that will complicate planning U.S. national security policy in the Information Age.
The Information Warfare Threat
Most Americans are familiar with how the information revolution has produced unprecedented improvements in economic efficiency and productivity. However, they are only just becoming aware of how much the information revolution has made the United States and other advanced economies dependent on computers, software, and communications systems. Dependence usually means potential vulnerability. This is why strategic thinkers have begun to worry about the threat of “information warfare,” or, to use the inevitable Pentagon abbreviation, IW.
Information warfare can include traditional tactics like psychological operations or electronic jamming. But in the Information Age, it will also likely include various forms of “computer network attack”—hacking to achieve military objectives.
To understand how a computer network attack might work, recall the denial-of-services incident against Yahoo, eBay, E*Trade, and other Internet-based businesses in February 2000. A Canadian hacker infiltrated several unsuspecting, unprotected network servers. The virus transformed the servers into zombie vandals, which began to bombard computers at the targeted companies with thousands of bogus messages. Or recall the “Love Bug” virus incident just two months later. A Philippine computer student released a self-replicating attachment to an e-mail message that multiplied out of control, jamming the computers of millions of users worldwide. Indeed, hardly a week goes by without a report that hackers have penetrated some major organization’s computer system.
Now think of what might have happened if the instigator of such an attack was a hostile army or intelligence service, intent on hurting the United States. Such organizations have deep pockets. They could afford a staff of dozens or even hundreds of experts who know how computer networks work—and how to make them fail. They would probably time their attack and select targets to cause as much damage as possible. Most important, they would probably plan their attack to achieve significant political objectives and integrate it into a larger military operation or terrorist strike. That is the threat of computer network attack.
|
If a single computer hacker in Canada or the Philippines can wreak havoc on e-mail systems throughout the globe, imagine the harm a determined band of cyberterrorists could cause. |
Attacking an opponent’s computer networks is already becoming a routine—and important—component of modern warfare. During Operation Allied Force last spring, for example, U.S. forces reportedly inserted bogus data into Serbian air defense networks. Serbia itself tried some amateurish efforts to hack U.S. and NATO computer systems. As military organizations and economies worldwide become more dependent on information systems, these systems will become targets for attack.
Hostile nations are not the only concern. Even hostile nonstate actors, such as terrorist groups, have the capability to mount a significant IW threat. Indeed, the barriers to entry are low for IW, so such “cyberterrorism” may become the tactic of choice for such groups in the future.
The Primary Target: Commercial Systems
It is important to understand that the most likely targets of a future IW attack are nonmilitary computer systems. There are several reasons for this. Most information systems are operated by the private sector, not the government. If one were to use military jargon, one would say that the private sector offers a more “target-rich” environment. Commercial systems are also likely to be less protected. Military organizations assume foreign military forces will target their computer networks and prepare accordingly. Most companies are becoming more aware of threats by hackers and cybercriminals, but few probably consider that they might be in the gun sights of Saddam Hussein, Osama bin-Laden, or the People’s Liberation Army.
Also, military and commercial computer systems operate under different constraints. Military users are accustomed to the inconvenience of strict security measures. Commercial systems, in contrast, are designed mainly for convenience. Companies must compete for customers, and customers like computer services that are easy to use.
A successful strike would not only disrupt the economy but could cripple U.S. military forces. Although the defense department operates a large transportation and communications network of its own (e.g., the familiar Air Force cargo transports and MILSTAR relay satellites), most military transportation and communications use the same commercial services as the public. If an adversary were to attack these systems, U.S. military forces would find it much harder to reach the scene of a conflict and harder to operate once they arrived.
This is why attacks against commercial computer networks will likely become a routine part of planning military operations. Many foreign military leaders have already acknowledged that their countries are exploring how to use computer network attacks in wartime. The military literature in China, Russia, and India—to name just three countries—has frequent references to information warfare and the possibility of computer network attack.
Although these articles usually describe such attacks as potential threats from abroad, any military organization that writes about such a threat has probably considered developing similar capabilities for itself. Military writers often cite foreign threats so they can discuss topics without giving away their own plans or creating controversy. (Indeed, even U.S. defense officials spoke about defensive information warfare in unclassified channels several years before they openly discussed the possibility of American offensive IW operations.)
Strategic Information Dominance
As a result, the ability of the United States to protect itself against computer network attack depends heavily on the actions of the private sector. This is a new development, and it presents new problems.
In the past, the federal government could mainly act alone to prepare homeland defenses. During the nineteenth century, for example, the federal government built fortifications along the coast to defend against hostile naval forces. In the 1940s and 1950s, the federal government built an extensive air defense system to counter the threat of bomber attack. In these cases, companies in the private sector had a minor role, if any—usually as contractors taking direction from the government. Even civil defense was mainly a government-directed, government-implemented operation under the direction of the Federal Emergency Management Administration.
This is where Microsoft, its dominance in the software market, and the government’s antitrust action converge. Software is not just a CD one buys in a shrink-wrapped box at the store. Software has become part of the nation’s infrastructure. We communicate through it. We use software to store our wealth and maintain our records. Today software comprises the control levers that direct trains, planes, and factories.
Because most of this software is designed and produced commercially, it is little wonder that commercial software companies are key potential targets for attack. We are safer if these companies are U.S. based. To put it bluntly: we can be sure that Microsoft, IBM, Oracle, Novell, NCR, and other U.S. companies would not knowingly do anything to help a foreign adversary attack U.S. commercial computer systems. We cannot be certain that a foreign company would be so cooperative. That is why U.S. dominance of the global information industry—and, in particular, software—is one of our most important assets for national security. Imagine for a moment that the market for PC operating systems or Internet browsers were dominated by, say, a company based in France or India. Would Americans feel as secure when they logged on?
Probably not. It’s not that Microsoft would put a trapdoor in Windows to allow the U.S. government to spy on computer users or shut down foreign networks during wartime. (In fact, in November 1999 Microsoft and the National Security Agency spent much time debunking such a rumor.) But Microsoft is a U.S.-based company, subject to U.S. laws and regulations concerning computer privacy, liability, and security. These laws and regulations can, when properly used, result in commercial products that are more resistant to attack. Also, U.S. government agencies with expertise in building secure computer systems can cooperate more freely with American companies than they can with foreign companies.
From a national security perspective, the United States would be best off if American companies were dominant in all segments of the information industries. This may not be possible, but we can at least avoid policies that, in effect, penalize those U.S. companies that achieve dominance.
That is what is most troubling about the justice department’s proposed remedy. If adopted, it would establish a dangerous precedent. Rather than simply restraining Microsoft from engaging in unfair business practices and penalizing the company for past violations, the justice department intends to restructure the software market. The justice department lawyers proposed breaking up Microsoft in the name of increasing competition—that is, ending Microsoft’s dominance.
|
Breaking up Microsoft could create threats to U.S. national security that would outweigh any of the purported economic benefits. |
Even if one agrees that Microsoft has engaged in anticompetitive practices, that is not an argument for restructuring the software industry. Indeed, the government may be seeking an outcome that is not only ill conceived but unlikely to be achieved in any case.
Many experts believe that information technologies (at least in their current state) naturally result in one company winning a disproportionate share of the market. The benefits of standardized software are so great that, once a company achieves a critical mass of users, it attracts other users and dominates the market. Recent experience shows that this trend occurs not only in the software industry but in other sectors of the information industry. For example, Intel (microprocessors), Cisco (routers), and Oracle (database software) all have captured 80—90 percent of their respective markets.
Companies dominating their sector will continue to dominate the market until some major event shakes up the entire market. This could be a technology breakthrough, such as the introduction of the PC or the Internet. Or it could be an event imposed from outside—such as the justice department’s proposed action. If the courts go ahead with the breakup proposed by the justice department, we might have a chance to test this theory.
The justice department envisions that its proposal will lead to two U.S.-based firms: one inheriting Windows and its market; the other inheriting Office, Explorer, and other Microsoft applications and their markets. Unfortunately, it is hard to predict what will really happen. Dominance of the information industry is just about impossible to predict (just ask IBM, Control Data, and Sperry Univac), especially in the software sector (witness WordPerfect, Lotus, and VisiCalc).
Foreign software firms already dominate or have a strong presence in several market sectors, including Germany’s SAP in business applications and Canada’s Corel in graphics and word processing. Indeed, the concept for the World Wide Web was originally developed in Switzerland. Developers in Finland lead the world in applications for Wireless Applications Protocol, the programming language that could become the basis for mobile Internet devices. The foreign presence is even stronger behind the scenes, where Indian and Israeli companies serve the world as programming outsourcing shops. All these companies are potential competitors—which is to say potential threats to U.S. dominance.
Misguided efforts to limit Microsoft—or any other U.S. company—could open an opportunity for a foreign firm. Market dominance in the Information Age will always be tough to achieve, and the U.S. government cannot guarantee that American firms will prevail. But why would we want to make the odds higher than they otherwise might be? Indeed, in its proposal to break up Microsoft, the justice department implicitly suggested that it would be willing to accept foreign competition as a remedy for Microsoft’s market dominance. This would increase the potential risks to U.S. national security.
Government and Industry
Yet the government’s proposal for breaking up Microsoft is really just a symptom of a larger problem. Recent government policies for regulating information technology industries have often run counter to U.S. national security interests. For example:
-
Like Microsoft, Intel has been warned that it might be the target of an antitrust action. Intel’s transgression is that it dominates the market for microprocessors used in personal computers. Ironically, it was only about 10 years ago that pundits warned that Japanese firms had captured a similar share of the market for memory chips and that this was a threat to national security because it made the United States dependent on foreign suppliers.
-
U.S. immigration controls restrict the number of workers who can enter the country to take research and software development jobs in our information technology industries. In addition to raising costs, this policy, in effect, encourages U.S. companies to outsource code from abroad, rather than allow the programmers to work in the United States. It would be better from a security standpoint for the companies to develop the code here, where corporate management and the U.S. government would have greater control.
-
The United States delayed relaxing restrictions on encryption until early this year. Restrictions on encryption were an especially misguided policy–they not only encouraged competition from foreign companies, who could sell software that was more secure than that offered by their U.S. competitors, but also made it harder for U.S. companies to make software that was resistant to IW attack. Although encryption does not make computer systems invulnerable to attack, it is almost impossible to make secure software without strong encryption.
It is odd that no one seems to have thought much about how a breakup of Microsoft might affect U.S. security. National security was a major issue when, for example, the government pursued its antitrust case against AT&T in the early 1980s. AT&T had worked closely with the defense department on telecommunications issues. Officials made sure that security issues were addressed even when the company was broken up in 1984.
The stakes for national security could be much greater in the Microsoft case than they were in the AT&T settlement. It was unlikely that a foreign company would take over the physical plant AT&T had built in the United States. It is much more plausible that, if Microsoft loses its dominant position, the software U.S. consumers choose could be the product of a foreign competitor.
The ability of the United States to defend itself from a future IW attack will depend much on the market strength of U.S. firms in the information industries. We need to think about the effect of a misguided antitrust settlement on national security. To paraphrase Georges Clemenceau, software is much too important to be left to the lawyers.